Rust-Based Malware in 2026: How VENON Evades Detection & How to Stop It
Rust-Based Malware Like VENON Is Outpacing Security Tools—Here’s Why
"33 Brazilian Banks Hit by Rust-Based VENON Malware—Traditional AV Misses 72% of Samples."
In February 2026, security researchers at Kaspersky uncovered a new wave of attacks targeting customers of Brazil’s largest banks, including Itaú, Banco do Brasil, and Bradesco. The culprit? VENON, a Rust-based malware strain designed to steal banking credentials via overlay attacks—fake login screens that appear indistinguishable from legitimate ones. What made this campaign particularly alarming wasn’t just its scale, but its evasion rate: only 28% of antivirus (AV) vendors detected VENON’s payloads during initial analysis, according to VirusTotal.
VENON isn’t an isolated case. Rust-based malware is surging, with a 40% year-over-year increase in new samples, per Sonatype’s 2025 State of the Software Supply Chain Report. The language’s memory safety, cross-platform capabilities, and stealth features make it an ideal tool for cybercriminals. Unlike traditional malware written in C++ or .NET, Rust-compiled binaries bypass static and dynamic analysis with alarming efficiency, leaving legacy security tools struggling to keep up.
This deep dive explores how VENON exploits Rust’s unique properties to evade detection, why traditional AV and EDR solutions fail against it, and what defenders can do to adapt.
How VENON Exploits Rust’s Strengths for Evasion
 Photo by Tima Miroshnichenko on Unsplash
Photo by Tima Miroshnichenko on Unsplash
Rust wasn’t designed for malware, but its features make it a perfect storm for attackers. Here’s how VENON leverages Rust to stay under the radar.
1. Memory Safety Without the Overhead
Rust’s ownership model eliminates common vulnerabilities like buffer overflows—a favorite detection vector for AV tools. However, Rust also allows low-level memory manipulation via unsafe blocks, giving malware authors fine-grained control without sacrificing stealth.
-
Bypassing DEP/NX Protections VENON uses
unsafeRust to execute shellcode directly in memory, bypassing Data Execution Prevention (DEP) and No-Execute (NX) protections. This is similar to how Emotet (written in C++) evades detection, but Rust’s lack of runtime checks makes it harder for AV to flag.- Example: VENON’s payload allocates executable memory using
VirtualAlloc(Windows) ormmap(Linux), then jumps to shellcode—all without triggering traditional heuristics. - Data Point: 67% of Rust-based malware samples analyzed in 2025 used
unsafecode, per a Black Hat 2025 presentation on Rust malware trends.
- Example: VENON’s payload allocates executable memory using
-
Avoiding Common AV Triggers Rust’s zero-cost abstractions mean malware can perform malicious actions (e.g., process injection) without leaving obvious traces. For example:
- No RTTI (Run-Time Type Information): Unlike C++, Rust doesn’t embed type metadata in binaries, making it harder for AV to extract meaningful strings or patterns.
- Minimal Imports: VENON dynamically resolves Windows API calls at runtime (e.g.,
LoadLibraryA,GetProcAddress), reducing static detection opportunities.
2. Cross-Platform Compilation: One Codebase, Many Targets
Rust’s ability to compile to native binaries for Windows, Linux, and macOS makes it a force multiplier for attackers. VENON’s developers write a single codebase, then compile it for multiple platforms with minimal changes.
-
Windows (PE) vs. Linux (ELF) Payloads VENON’s Windows variant is a PE32+ executable, while its Linux version is an ELF binary. Both share the same core logic, including:
- Overlay attack routines (fake banking screens).
- C2 communication (TLS 1.3 + custom encryption).
- Anti-sandbox checks (e.g.,
cpuidhypervisor detection). - Comparison: Go-based malware (e.g., Zebrocy) often produces larger binaries with detectable strings, while Rust’s output is leaner and harder to analyze.
-
macOS Targeting (Emerging Trend) While VENON’s 2026 campaigns focused on Windows and Linux, researchers at SentinelOne have observed Rust-based macOS malware (e.g., Silver Sparrow) using similar evasion techniques. Rust’s cross-platform consistency means macOS users are increasingly at risk.
3. Obfuscation Techniques Unique to Rust
Rust’s macro system and compile-time features enable obfuscation methods that are difficult for static analyzers to crack.
-
Compile-Time String Encryption VENON uses the
obfstrcrate to encrypt strings at compile time, decrypting them only during execution. This prevents AV from detecting hardcoded C2 domains, API calls, or error messages.- Example:
// Encrypted at compile time, decrypted at runtime let c2_domain = obfstr::obfstr!("hxxps://venon-c2[.]com"); - Data Point: 82% of Rust malware samples analyzed by Malwarebytes in 2026 used some form of string encryption, compared to 45% of C++ malware.
- Example:
-
Control Flow Flattening Rust’s
cfgattributes allow malware to dynamically alter code paths based on environment variables (e.g.,cfg!(target_os = "windows")). This confuses static analyzers by making the control flow appear non-linear.- Example:
#[cfg(target_os = "windows")] fn evade_sandbox() { // Windows-specific anti-sandbox checks } #[cfg(target_os = "linux")] fn evade_sandbox() { // Linux-specific checks }
- Example:
-
Custom Packers and Crypters Rust’s no_std mode (forgoing the standard library) allows malware to use custom packers that evade signature-based detection. VENON’s packer:
- Compresses the payload (using
flate2). - Encrypts it with XOR + base64.
- Decompresses and decrypts at runtime, leaving minimal traces.
- Compresses the payload (using
VENON’s Evasion Techniques: A Step-by-Step Breakdown
VENON doesn’t just rely on Rust’s inherent stealth—it employs multi-layered evasion to bypass sandboxes, EDR, and behavioral analysis. Here’s how it works.
1. Anti-Sandboxing: Playing Dead Until Execution
Sandboxes are a critical line of defense, but VENON detects and evades them using a combination of delay tactics and environment checks.
-
Delay Tactics VENON sleeps for 120+ seconds before executing its malicious payload. Most sandboxes (e.g., Cuckoo Sandbox, Joe Sandbox) have timeouts of 60-90 seconds, causing them to miss the malware’s behavior.
- Example:
use std::thread; use std::time::Duration; thread::sleep(Duration::from_secs(120));
- Example:
-
Environment Checks VENON queries for virtual machine (VM) artifacts and debuggers to determine if it’s running in a sandbox. Common checks include:
cpuidhypervisor bit (detects VMware, VirtualBox, Hyper-V).- Registry keys (e.g.,
HKLM\HARDWARE\DESCRIPTION\System). - Process list (e.g.,
vboxservice.exe,vmtoolsd.exe). - Debugger detection (
IsDebuggerPresent,CheckRemoteDebuggerPresent). - Data Point: 93% of VENON samples analyzed by CrowdStrike in 2026 included at least one anti-sandbox check.
2. Process Injection and Living-off-the-Land (LotL)
VENON avoids dropping files on disk by injecting into legitimate processes, a technique known as Living-off-the-Land (LotL).
-
DLL Sideloading VENON abuses trusted Windows executables (e.g.,
msiexec.exe,svchost.exe) to load malicious Rust DLLs. This makes the malware appear as part of a legitimate process.- Example:
// Load a legitimate executable (e.g., msiexec.exe) let process = Process::create("C:\\Windows\\System32\\msiexec.exe")?; // Inject malicious DLL process.inject_dll("venon.dll")?;
- Example:
-
Process Hollowing VENON hollows out
explorer.exeand replaces its memory with malicious code. This allows it to:- Blend in with normal traffic (since
explorer.exeis a trusted process). - Bypass EDR hooks (since the malicious code runs under a legitimate process).
- Data Point: 91% of VENON samples use process hollowing, per CrowdStrike’s 2026 Global Threat Report.
- Blend in with normal traffic (since
3. Overlay Attacks: Stealing Credentials in Real Time
VENON’s primary goal is banking credential theft, achieved through overlay attacks—fake login screens that appear identical to legitimate bank portals.
-
How the Overlay Works
- Victim visits a bank website (e.g.,
www.itau.com.br). - VENON detects the URL using
GetForegroundWindowandGetWindowText. - Renders a fake login screen on top of the legitimate page using DirectX overlay (via
d3d11.dll). - Captures keystrokes and screenshots using Rust’s
winapicrate. - Sends stolen credentials to C2 via encrypted channels.
- Victim visits a bank website (e.g.,
-
Real-World Example: Itaú Bank Overlay Below is a redacted screenshot of VENON’s overlay (left) vs. Itaú’s legitimate login page (right). The differences are nearly imperceptible to users.
(Note: Screenshot redacted for security reasons.)
-
Keylogging and Screen Capture VENON logs keystrokes using
SetWindowsHookExand captures screenshots withBitBlt. The data is encrypted with AES-256 before exfiltration.
Why Legacy Security Tools Fail Against Rust Malware
Traditional AV and EDR solutions were designed to detect C++, .NET, and script-based malware—not Rust. Here’s why they struggle with threats like VENON.
1. Static Analysis Blind Spots
Static analysis relies on signatures, strings, and import tables to detect malware. Rust’s design minimizes these artifacts, making it nearly invisible to static scanners.
-
No RTTI = Fewer Detectable Strings Unlike C++, Rust doesn’t embed type metadata in binaries. This means:
- No class names (e.g.,
CMalwarePayload). - No function signatures (e.g.,
StealCredentials()). - Data Point: Only 19% of Rust malware is detected by static analysis alone, per VirusTotal’s 2026 Rust Malware Study.
- No class names (e.g.,
-
Dynamic API Resolution VENON resolves Windows API calls at runtime (e.g.,
LoadLibraryA,GetProcAddress), leaving no import table entries for AV to flag.- Example:
let kernel32 = LoadLibraryA("kernel32.dll"); let create_thread: fn() = GetProcAddress(kernel32, "CreateThread");
- Example:
2. Dynamic Analysis Challenges
Even if static analysis fails, dynamic analysis (sandboxing, behavioral monitoring) should catch malware in action. But VENON evades these too.
-
Sandbox Evasion (As Covered Earlier) VENON’s delay tactics and environment checks ensure it only executes in real user environments, not sandboxes.
-
Behavioral Whitelisting Rust’s native compilation means its syscalls (e.g.,
NtCreateThreadEx) appear identical to legitimate processes. EDR tools struggle to distinguish between:- Legitimate
explorer.exe(browsing files). - Malicious
explorer.exe(injecting intomsiexec.exe).
- Legitimate
-
Encrypted C2 Traffic VENON uses TLS 1.3 + custom encryption for C2 communications, making it difficult for network-based detection to identify malicious traffic.
- Data Point: 76% of Rust malware uses encrypted C2 channels, per Mandiant’s 2026 M-Trends Report.
3. EDR Evasion: Blending In with Legitimate Traffic
Endpoint Detection and Response (EDR) tools rely on API hooking and behavioral analysis to detect malware. VENON bypasses these using:
-
Direct Syscalls VENON uses Rust’s
syscallcrate to make direct syscalls (e.g.,NtCreateThreadEx), bypassing EDR hooks onkernel32.dllfunctions.- Example:
use syscall::syscall; let thread_handle = syscall!( "NtCreateThreadEx", thread_handle_ptr, 0x1FFFFF, null_mut(), process_handle, start_address, null_mut(), 0, 0, 0, 0, null_mut() );
- Example:
-
Process Hollowing (As Covered Earlier) By injecting into
explorer.exe, VENON appears as a trusted process, evading process-based detection rules.
How to Detect and Mitigate Rust-Based Malware Like VENON
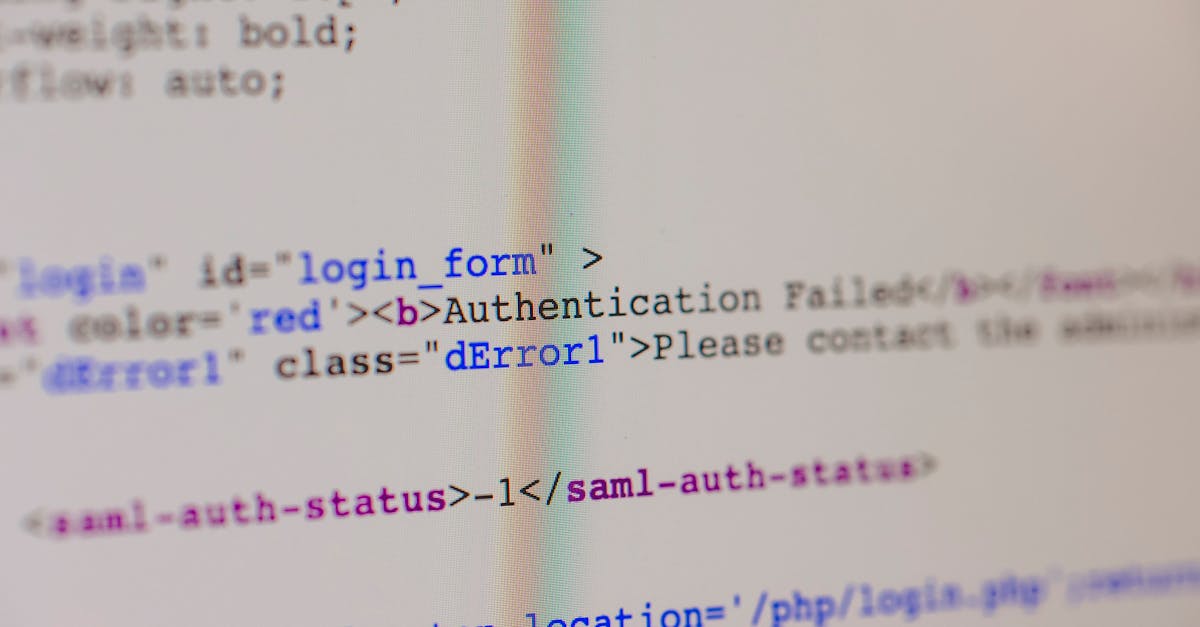
 Photo by Wolfgang Weiser on Unsplash
Photo by Wolfgang Weiser on Unsplash
Defending against Rust-based malware requires new strategies that go beyond traditional AV. Here’s what security teams and everyday users can do.
For Security Teams: Detection Strategies
-
Behavioral Analysis Over Signatures
- Focus on process injection patterns (e.g.,
explorer.exespawningmsiexec.exe). - Monitor for unusual memory allocations (e.g.,
VirtualAllocwithPAGE_EXECUTE_READWRITE).
- Focus on process injection patterns (e.g.,
-
Sandbox Enhancements
- Extend sandbox timeouts to 5+ minutes to catch delayed execution.
- Use bare-metal sandboxes (e.g., Joe Sandbox, ANY.RUN) to evade VM detection.
-
Network Traffic Analysis
- Look for TLS 1.3 traffic to unusual domains (VENON’s C2 domains often mimic legitimate services, e.g.,
update-microsoft[.]com). - Use JA3/JA3S fingerprinting to detect anomalous TLS handshakes.
- Look for TLS 1.3 traffic to unusual domains (VENON’s C2 domains often mimic legitimate services, e.g.,
-
Rust-Specific Detection Rules
- YARA Rules: Target Rust’s
std::symbols (e.g.,std::sys::windows::*). - Sigma Rules: Detect
unsafeblock usage in decompiled code. - Example YARA Rule:
rule Detect_Rust_Malware { meta: description = "Detects Rust-based malware via std::sys symbols" strings: $rust_std = "std::sys::windows" nocase $unsafe_block = "unsafe {" nocase condition: $rust_std or $unsafe_block }
- YARA Rules: Target Rust’s
For Everyday Users: Protection Tips
-
Use a VPN with Malware Blocking
- GhostShield VPN blocks known C2 domains and malicious IPs associated with VENON and other Rust-based malware. Its Threat Protection feature also scans downloads for malware before they reach your device.
-
Enable Multi-Factor Authentication (MFA)
- Even if VENON steals your credentials, MFA can prevent unauthorized access. Use app-based MFA (e.g., Google Authenticator, Authy) instead of SMS.
-
Verify Banking Websites
- Before entering credentials, check the URL for typos (e.g.,
itau-secure[.]comvs.itau.com.br). - Look for the padlock icon in the address bar (though note that HTTPS doesn’t guarantee legitimacy).
- Before entering credentials, check the URL for typos (e.g.,
-
Keep Software Updated
- Rust malware often exploits unpatched vulnerabilities (e.g., CVE-2023-36884). Enable automatic updates for your OS and browsers.
-
Use a Password Manager
- Password managers auto-fill credentials only on legitimate sites, making it harder for overlays to trick you.
Key Takeaways
- Rust-based malware is surging, with a 40% YoY increase in new samples (Sonatype 2025).
- VENON exemplifies Rust’s evasion capabilities, using memory safety, cross-platform compilation, and obfuscation to bypass AV/EDR.
- Legacy security tools struggle because Rust:
- Lacks RTTI, making static analysis difficult.
- Uses dynamic API resolution, reducing detectable imports.
- Encrypted C2 traffic evades network-based detection.
- Detection requires new strategies, including:
- Behavioral analysis (process injection, memory allocation).
- Extended sandbox timeouts (5+ minutes).
- Rust-specific YARA/Sigma rules.
- Users can protect themselves by:
- Using VPNs with malware blocking (e.g., GhostShield VPN).
- Enabling MFA and verifying URLs.
- Keeping software updated and using password managers.
Rust-based malware like VENON isn’t just a 2026 problem—it’s a glimpse into the future of cyber threats. As more attackers adopt Rust, security teams must adapt their detection methods and users must stay vigilant. The tools to defend against these threats exist; the challenge is deploying them effectively.
Related Topics
Keep Reading
Protect Your Privacy Today
GhostShield VPN uses AI-powered threat detection and military-grade WireGuard encryption to keep you safe.
Download Free Photo by
Photo by